Nightmare on LAN Street
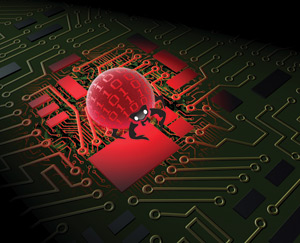 Somewhere, at this very moment, devious criminal minds are hard at work conspiring at computer stations.
Somewhere, at this very moment, devious criminal minds are hard at work conspiring at computer stations.
As you read this article consider this fact: Somewhere, at this very moment, devious criminal minds are hard at work conspiring at computer stations. They are compulsively targeting you as their next victim. Everyday, there are multitudes of sociopaths all over the world designing assaults devoid of empathy, thus placing everyone’s technology networks in jeopardy.
It is not a matter of if. It is a matter of when.
The nightmare
Imagine what would happen if all the computers in your organization suddenly stopped working and there was no way of retrieving stored data. Imagine the intruders had also compromised your backup systems as a part of their overall tactical strategy. If that does not put you into a cold sweat, imagine your phone systems suddenly become inoperative. What would it be like if there was no way to retrieve your customer base, collect receivables, pay bills, make sales or do payroll? Many businesses have come to realize this nightmare can be real. All it takes is for an employee to innocently open an attached file on a seemingly safe parcel of e-mail. Without the proper protection, this can unleash a swift spreading malignancy upon your company’s computer network system. As we become more dependent on technology, we become more vunerable to the Techno Ne’er-do-wells.
How it all began
It’s been more than 25 years since the first computer-born virus was introduced in January of 1982. The Elk Cloner Virus, designed to jump from one Apple workstation to the other, was designed by a 15-year-old gamer named Rich Skrenta. It is estimated that as many as one million viruses infect the world’s technology networks. Propagation estimates hypothesize the total number of techno-pathogens are now doubling nearly every 12 months.
The battle line is drawn
It is a full-time endeavor protecting computers & LANs (Local Area Networks) from high tech’s darker side. There are highly intelligent designers working either side of the equation; those who perpetuate misery and those who defend the world against it. It’s mind boggling how many hacking thugs and viral engineers there are in existance. From their wake, a multibillion dollar network defense industry has emerged. As a result, an arsenal of products have been developed to help defend organizations and individuals against this ever mounting onslaught. It has become critical for businesses to know where their exposures are and how to defend against them. Lately, there has been a great deal of media attention devoted to the perils corporate technology networks are confronted with, and the risks facing the data they contain.
The enemy
The most common misunderstandings regarding network security are knowing where the areas of exposures are and how to defend against them. When you consider the sheer volume of viruses, trojans, spyware, adware, worms and other various forms of ticking time bombs, you may never download anything ever again. For every cure discovered there are two new infections created. This battle will never be won, it will always be fought.
Let us begin by looking at the three primary categories of exposure/risk:
- Infections: The Invading Organisms
- Hackers: The Burglars (Breaking & Entering)
- Internal Exposures: The Trusted Saboteurs
It is not a coincidence that network infections and biologic infections share similar medical monocultures including terms such as disinfect antivirus and de-worming. Defining what an infection is makes the correlation undeniably congruous.
Infection
Infections are invasive organisms (biopathogens) that require a host to survive, reproduce and multiply with an eventual goal of spreading to other hosts.
The end of the world
Some of the world’s most respected biologists have predicted the end of the world would be born of a virus. Considering the impact network viruses (techno-pathogens), in conjunction with hackers, potentially pose to national defense systems, the bioscientists may have it partially correct. However, the real doomsday virus might not be biologic in nature.
Morphology
There is little difference in the morphology of biologic infections found in living organisms and infections found invading technology networks. Some infections are relatively benign, having little or no impact on the host. They often go undiscovered. A biologic and network infection’s impact on the host can range in severity from no impact, to moderately debilitating. They can be paralytic and some are even lethal. Both can catastrophically proliferate if left un-quarantined, especially when inoculations are forsaken. There is pandemic risk associated with both biopathogens and techno-pathogens; they can rapidly spread across the planet if left unchecked leaving devastation in their wake.
Proliferation
Computer/network and biologic infections are identical twins for a reason. The designers of techno-pathogens exploited the devastating success nature’s pathogens had already shown the world. After all, the terms “plagues” and “pandemics” are classifications of extraordinarily successful infections. Criminals producing computer/ network infections try and design them based on nature’s most successful designs. This is why biopathogens and network pathogens similarly hide, mutate, attack, reproduce and spread to other hosts. Another similarity is that they often mutate inside of a preliminary host, and use this process as a stepping stone to ultimately attack the next host who was the initial intended victim. This concept was an underlying theme in the series of “Alien” movies in which Sigourney Weaver played one of the hosts infected by a creature. The species mutated inside the first victim (host) in order to ultimately reach the next phase of the creature’s destructive evolution. There are a growing number of computer-born infections that tactically mutate.
Dangerously smart bugs
Some biologic infections aren’t directly damaging to the host and have little direct negative impact. However, they can weaken immune systems allowing a secondary invasion of infecting organisms that directly attack the host. With a weakened immune system, the second invading organisms produce devastating consequences. HIV is an obvious example of this. The truth is, no one has directly died from HIV or AIDS. Millions have died as a result of secondary infections that exploited the weakened immune system caused by HIV. There are multi-viral attacks on computer networks that essentially do the same thing. First, they cripple antivirus protections and/or firewalls and are quickly followed by a secondary line of attacks designed to exploit weakened protections. Another sickening similarity to HIV is that some criminal engineers design their computer pathogens to mutate as they spread, making them hard to vaccinate.
Laying in wait
Biopathogens can lay dormant for years, waiting for the right conditions before they acutely attack their host. Pathogens such as Leprosy, Cancer, HIV, Hepatitis-C and Tuberculosis all fall into this group. Many of the trojans and worms fall into this group too; they often hide, and assimilate the appearance of legitimate files. They wait in dormancy for the right conditions to trigger the aberrant program to springboard into attack.
Burglars were once referred to as hackers because they physically hacked their way into restricted places. Therefore, it’s not a coincidence that the term has been adopted by IT.
Burglary
Burglary is the act of breaking and entering into another’s property with the intent to steal or commit vandalism.
Break-ins
Hackers are the burglars of the IT world. They break and enter with the intent to steal data and vandalize networks. Hackers are merely criminals despite the many attempts to romanticize them as misunderstood intellects. Burglars have complete disregard for other people’s property as well as the pain and expense they perpetrate on others. Hackers’ negative impacts on society cause loss of employment, loss of philanthropic resources, damage to national security and put the research and development of life saving medicine at risk. The worst self-imposed entitlement is one that can cause loss of life and it is unfortunate that some Internet countercultures and movies euphemistically try to glorify these criminals.
In battle, the biggest area of risk is the quarter most overlooked
All risks left unconsidered will thereby become the least defended. This is due to the nearly infinite variables associated with exposure. The War in Iraq is an example of a battle in which the largest area of risk was not well planned for. Regardless of your political stance, the cause and effect has been evident. Simply put, exposure is almost always self-induced.
Internal exposure
Any discussion of network security needs to include a section regarding the internal risks. Corporate executive leadership is often lulled into believing that if the antivirus software is up-to-date, all is well. What about Mr. Computer Guy with the thick glasses whose hands are tightly wrapped around one of the company’s vital organs? The very nature of an IT employee’s work grants him or her access to most of the company’s confidential information and secrets. An IT employee’s job also gives him or her the opportunity to copy, disseminate, alter or destroy the same data. The accessibility granted to the technology staff, in combination with their technical prowess, enables a quick and effective conduit to sabotaging entire networks. It isn’t difficult for most IT staff members to hack in and invisibly write company checks.
As long as I am scaring the “bejeebies” out of you, your phone systems aren’t immune from maliciousness either. IT staff can certainly disable antivirus and take out firewalls with the pull of a cord, destroying your company’s immune system. IT is not the only source of internal network insecurity, but it is usually the greatest point of exposure when checks and balances are not in place.
Gatekeepers
The problem is, sooner or later, you have to trust somebody, and you absolutely have to trust your IT staff. Therefore, it is essential to perform an extensive background check on anyone associated with this critical point of exposure. It is surprising how many executives blindly trust the geek with a pocket protector. It is ironic that the IT staff is entrusted with protecting the organizations they work for. Someone needs to be able to use technology to control various levels of access to data according to what should be allowed or disallowed. The IT staff generally become the gatekeepers because technology is used in controlling permissions. From their mighty pocket protectors, IT staff adjusts limits (referred to as permissions) to confidential materials via network databases. Of course, they are responsible for protecting all the other points of security exposure including, but not limited to, Internet, intranet and VPN. Trustworthy IT staff will jealously protect their company’s network. They often inconvenience everyone with over-conservatism. This is the mindset you are looking for! IT staff must police the company from its own members, and likewise, the company needs to protect itself from its IT staff. The latter recommendation is often overlooked.
Counter-measures
Research to fend off bio-attacks is nearly identical to the methods associated when designing an antivirus for technology networks. It is no coincidence that both approaches are performed in labs with similar controls; after all, the pandemic threat from inaction has global similarities for both. There is little attention paid to this threat outside the specialty as the world doesn’t give it much consideration. The damage caused by network infections and hackers places lives and nations at risk and can be financially catastrophic. The men and women fighting the good fight understand they have a moral responsibility to protect the world against these vulnerabilities. It should not be surprising that their mindsets are similar to research biologists.
Preventative medicine
The two ways people protect themselves from getting sick are avoiding infections and strengthening their immune systems.
The two ways computer networks protect themselves from getting sick are avoiding infections and strengthening their immune systems.
Avoidance
Clearly, proactive avoidance requires an understanding of where infections get introduced. The following are common ways for a network to become infected: opening unfamiliar contaminated attachments, clicking on suspect links within e-mails, clicking on suspicious execution buttons or links while surfing, downloading anything suspect or unknown, using un-keyed wireless routers and connecting to weakly encrypted “Hot Spots” on company-owned laptops. You should consider anything Internet pornography related as contaminated and extremely dangerous. Pornographic sites, links and downloads are virulently infested with adware and viral devices designed to take control of your network and/or computer.
Rumor has it glancing at a coworker’s inappropriate screensaver can damage your car’s transmission. Even though this is an obvious exaggeration, a single screensaver procured from an unsafe source can cost a company millions of dollars in lost productivity and repairs when the network is not properly protected. Never click on a popup auto-executable. You might as well pull out a gun and shoot your hard drive.
Protecting your company’s network
When computer networks become infected, the network is essentially catching a disease. The first line of defense, as with children is inoculation through vaccinations. Diseases such as smallpox and polio were global plagues at one time. Today, these same diseases have nearly been eradicated because of immunization controls. Other infections such as influenza mutate with such frequency that a single vaccination won’t protect indefinitely. This is why an annual flu shot is required for those wanting to remain protected. Last year’s flu shot is normally not going to provide much protection for next year’s flu season. The same holds true for computer-driven networks. They must undergo a constant battery of vaccinations to protect against the ever growing number of techno-pathogens being designed by your neighbor’s kid working in his basement. The nonstop torrent of fresh computer-born infections introduced is the reason for those periodic (or annoying) messages advising you to update your computer. These messages are similar to those from your doctor’s office informing you that it’s time to get your flu shot. A word to the wise: listen to your doctor!
The hard & soft of it
Infection and break-in protections come in software and hardware formats and combinations of the two. Software-based solutions from Symantec and McAfee® are examples of quality, stand-alone software, and are among the most commonly used defenses to protect LANs and their computer counterparts. Antivirus software works by scanning, filtering, repairing, quarantining and/or redirecting to Internet sites to update protections or do Web-based repairs. Basically, the software investigates network and computer drives and the files contained (in some cases including firmware), scrupulously searching for the harmful material imbedded in the nooks and crannies. Anti-viruses tirelessly hunt down deviant files, waiting in ready. In addition, the security software evaluates files you attempt to download. Most security software is designed to, when possible, employ proactive measures before infections can take root. All software solutions require periodic updates to remain current.
Burglar bars
Stand-alone software is not commonly used to defend against hackers/break-ins. Firewalls such as the Nortel and Cisco® series are forms of routers robustly engineered to keep the burglars out. Most routers divide networks and route traffic and are used to set up firewalls. Firewall routers are designed specifically to defend your network’s infrastructure and are the weapon of choice to keep burglars/hackers from breaking and entering.
Big brother
Filter hardware/software combinations such as Barracuda and Spam Cube™ utilize a dedicated server approach loaded with software to coincide with a specialized architecture. Filters offer a stronger front line to protect against infection, and generally have more configurable global settings and e-mail protections in conjunction with LAN monitoring gadgets. LAN monitoring provides businesses with other security benefits. Depending on the version and strength of the hardware/software, LAN monitoring can enable system administrators to see how much time employees spend surfing, and where they surf, in addition to what they are streaming, downloading and purchasing. LAN monitoring can also monitor and identify who users are e-mailing and receiving mail from; it can monitor IM traffic as well. More powerful, higher-end LAN monitors will record and save keystrokes at workstations selected for scrutiny. Unfortunately, rouge proxy servers from competing companies can hack into your system and record all of these same actions. This presents an issue regarding the necessity for robust firewalls— especially if your business’ value is tied to intellectual, confidential assets.
Policing police
Think of the men in missile silos holding the nuclear keys—no single missile technician can launch by themselves. Activity recording software such as DB Tracing can record all database entries and modifications. Other forms of software can record the footprints of activity while associating it to the username logged in. Logins should have prescribed system permissions. The username at log in will prompt the network administrative protections to limit where the user can go and what the user can do. The limits are defined by a trusted senior system administrator. Even the senior system admin should be kept in check regarding tracing software, and policed by peers who have dissimilar access roles. Super confidential information should be stored on an insulated and completely quarantined encrypted workstation that has no Ethernet or wireless network capability. It should also have a removable hard drive that goes into a safe or goes home with the user at the day’s end.
What’s up with that…
Many have asked why technology criminals endeavor with such ferocity. There is little or no financial reward especially when you consider the insane amount of work that goes into their illicit activities. These criminals display astonishing intelligence yet risk spending many decades, if not the rest of their lives, in federal penitentiaries.
Computer-born viruses are plagues upon computer-driven networks. Their designers are plagues upon society.